Night Below PDF: A Comprehensive Guide (Updated 12/22/2025)
Night Below’s PDF availability is extensive‚ offering free downloads and Patreon access to maps; it’s a large campaign needing organization‚ split into sections for ease․
The adventure‚ originally published by TSR‚ is now readily available as a PDF file‚ with options for single-page processing and zipped downloads․
Numerous sources provide access‚ including direct downloads and community contributions‚ ensuring adventurers can easily embark on this Underdark journey․
Overview of Night Below
Night Below‚ a classic Dungeons & Dragons adventure‚ plunges players into the perilous depths of the Underdark․ Originally released by TSR‚ this expansive campaign‚ now widely available as a PDF‚ challenges parties from levels 1-10․
The adventure’s scope is immense‚ demanding numerous sessions to complete‚ hence the need for organized PDF sections․ Players navigate a complex web of factions and creatures‚ facing unique environmental hazards․ Accessing the PDF is straightforward‚ with options ranging from official sources to community-driven platforms and Patreon support․
It’s a truly immersive experience‚ demanding careful character preparation and strategic gameplay․
What is “Night Below”?
Night Below is a sprawling Underdark campaign adventure originally created for Advanced Dungeons & Dragons․ Now commonly distributed as a PDF‚ it’s a lengthy undertaking‚ requiring significant player commitment․ The adventure centers around exploration‚ political intrigue‚ and survival within the dangerous subterranean realm․
The PDF format allows for easy access and organization of the campaign’s numerous components․ It’s a classic example of dungeon crawling‚ featuring iconic Underdark locations and challenging encounters․ Freely available downloads and Patreon options enhance accessibility․
The Campaign’s Scope and Complexity
Night Below‚ available as a comprehensive PDF‚ is a substantial campaign demanding numerous gaming sessions․ Its scope is immense‚ encompassing a vast portion of the Underdark and intricate political landscapes․ The adventure’s complexity stems from the interwoven factions and challenging encounters within this subterranean world․
The PDF version aids organization‚ often split into sections for manageable gameplay․ Players will navigate treacherous environments and engage in strategic combat‚ requiring careful preparation and resource management․ It’s a truly epic undertaking․
Accessing Night Below: PDF Downloads
Obtaining the Night Below PDF is surprisingly accessible today․ Numerous online sources offer downloads‚ ranging from direct links to community-maintained archives․ Several websites provide the adventure as a PDF file‚ often with options for single-page or zipped formats for convenience․
Furthermore‚ platforms like Patreon host creators offering enhanced PDF versions‚ including high-resolution maps․ These resources streamline preparation and enhance the immersive experience of this classic Underdark campaign;
Official PDF Sources
Determining truly “official” Night Below PDF sources proves complex‚ given its age and history․ While TSR‚ the original publisher‚ no longer directly distributes it‚ digital storefronts sometimes offer authorized versions․ However‚ verifying authenticity can be challenging․
Currently‚ there isn’t a single‚ definitive official online source․ Players often rely on reputable Dungeons & Dragons resource sites and community archives‚ exercising caution regarding file integrity and legality when downloading․
Free PDF Availability and Legality
Numerous websites offer Night Below as a free PDF download‚ but accessing these raises significant legality concerns․ As the adventure is still under copyright‚ unauthorized distribution constitutes infringement․ While widely available‚ downloading from unofficial sources carries legal risks․
Supporting creators is crucial; consider purchasing official versions when available․ Exploring Patreon options‚ as mentioned‚ provides a legal avenue for accessing campaign materials and supporting content creators․ Prioritize ethical gaming practices․
Patreon and Alternative Download Options
Beyond potentially questionable free PDF sources‚ supporting creators offers legitimate access to Night Below․ Patreon emerges as a key alternative‚ with content creators providing downloadable maps – including high-resolution 8k versions – as rewards for patrons․
This method ensures you legally obtain campaign resources while directly supporting the community․ Exploring these platforms provides a win-win scenario‚ fostering continued content creation and offering adventurers quality materials․
Understanding the Underdark Setting
Night Below plunges adventurers into the perilous Underdark‚ a subterranean realm demanding adaptation․ This environment is uniquely challenging‚ characterized by perpetual darkness and a complex web of tunnels․ Success requires understanding the distinct factions vying for power – drow‚ duergar‚ and mind flayers – alongside the monstrous creatures inhabiting its depths․
Preparation is key; players must embrace stealth‚ navigate confined spaces‚ and anticipate constant threats within this unforgiving landscape․
The Underdark’s Unique Environment
Night Below’s Underdark is defined by its oppressive darkness‚ necessitating reliance on alternative senses and light sources․ The environment presents constant challenges: treacherous terrain‚ limited visibility‚ and the psychological impact of isolation․ Combat frequently occurs in confined spaces‚ demanding tactical adjustments․
Players must adapt to the lack of natural light‚ utilizing spells and equipment to navigate and survive․ The Underdark’s unique conditions fundamentally alter gameplay‚ emphasizing stealth and resource management․
Key Factions and Creatures within Night Below
Night Below features a complex web of Underdark factions‚ notably the Duergar of Gracklstugh and the Deep Gnomes of Mantol-Derith‚ locked in perpetual conflict․ Players will encounter a diverse bestiary‚ including Drow‚ Mind Flayers‚ and various monstrous denizens adapted to the darkness․
Understanding these factions’ motivations and the creatures’ behaviors is crucial for survival․ Alliances and betrayals are commonplace‚ demanding careful diplomacy and strategic combat planning within this dangerous realm․
Roleplaying Considerations for the Underdark
Night Below’s Underdark demands a shift in roleplaying focus․ Characters must contend with constant darkness‚ limited resources‚ and pervasive paranoia․ Trust is a rare commodity‚ and survival hinges on shrewd negotiation and cautious alliances․
Emphasize the psychological impact of prolonged isolation and the alien nature of the environment․ Consider how characters react to the Underdark’s unique cultures and the moral ambiguities inherent in its power struggles․
Character Preparation for Night Below
Preparing for Night Below requires careful consideration․ Recommended levels typically range from 1 to 10‚ demanding adaptable characters․ Optimal classes include rogues‚ rangers‚ and fighters‚ excelling in the Underdark’s challenges․
Races with darkvision are invaluable‚ alongside proficiency in stealth and survival skills․ Freyja‚ for example‚ prioritizes defensive castings like mirror image․ Prioritize spells and abilities that overcome darkness and navigate confined spaces‚ ensuring readiness for this perilous campaign․
Recommended Character Levels
Night Below is designed as a lengthy campaign‚ ideally suited for characters starting at 1st level and progressing to 10th․ This allows for significant character development within the Underdark’s harsh environment․
While higher-level characters could participate‚ they might diminish the campaign’s intended challenge and narrative arc․ Starting at a lower level ensures a gradual immersion into the setting and a more rewarding experience as characters overcome obstacles․
Optimal Character Classes and Races
For Night Below‚ classes excelling in stealth‚ survival‚ and combat within confined spaces are advantageous․ Rogues‚ Rangers‚ and Fighters are particularly well-suited․ Clerics and Paladins offer vital support against the Underdark’s dangers․

Dwarves‚ with their stonecunning and resilience‚ are naturally adapted; Gnomes possess inherent stealth abilities․ Humans offer versatility‚ while Half-elves provide a balance of skills․ Consider races with darkvision for navigating the perpetual darkness․
Essential Skills and Abilities
Navigating Night Below demands proficiency in Stealth‚ Perception‚ and Survival․ Knowledge skills like Arcana and History aid in understanding the Underdark’s lore․ Combat prowess is crucial; skills in Athletics and Acrobatics are beneficial for maneuvering in tight spaces․
Darkvision is paramount‚ alongside resistance to poison and psychic damage․ Spellcasters should prioritize illusion and enchantment magic․ Boltzolto’s defenses suggest preparation for magical and physical attacks․

Key NPCs in Night Below
Night Below features a complex web of characters․ Allies and enemies alike populate the Underdark․ Key figures drive the narrative‚ demanding careful interaction․ Understanding their motivations is vital for success․
Freyjand‚ a cleric‚ exemplifies a prepared adventurer‚ utilizing defensive castings like Mirror Image and Prayer․ Gracklstugh and Mantol-Derith harbor influential NPCs with hidden agendas‚ requiring astute roleplaying and strategic alliances․
Important Allies and Enemies
Night Below’s Underdark is rife with shifting allegiances․ Identifying trustworthy allies is crucial‚ though rare․ Enemies range from duergar slavers in Gracklstugh to monstrous creatures lurking in the shadows․
NPCs like Freyjand can offer aid‚ but even their motives require scrutiny․ The campaign demands players navigate treacherous relationships‚ discerning friend from foe․ Careful consideration of each encounter’s potential consequences is paramount for survival․
NPC Motivations and Backstories
Night Below’s depth lies in its complex NPCs․ Understanding their motivations—power‚ survival‚ or revenge—is key to successful interaction․ Freyjand‚ for example‚ prioritizes defense and prayer‚ hinting at a devout past or present danger․
Backstories are often shrouded in secrecy‚ requiring investigation․ Uncovering these narratives reveals hidden agendas and potential alliances․ Players must delve beyond surface appearances to truly grasp the Underdark’s inhabitants․
Interacting with Key Figures
Successfully navigating Night Below demands careful interaction with its NPCs․ Players should prioritize observation‚ discerning true intentions from veiled words․ Remember Freyjand’s defensive tactics; understanding his preparedness reveals a cautious nature․
Diplomacy‚ deception‚ and even combat may be necessary․ Each encounter presents unique challenges‚ requiring adaptable strategies․ Building rapport‚ or exploiting weaknesses‚ can significantly impact the campaign’s outcome․ Thorough preparation is crucial for meaningful engagement․
Major Locations within the Campaign
Night Below plunges adventurers into iconic Underdark cities like Gracklstugh‚ the City of Blades‚ and Mantol-Derith‚ the City of Chains․ These locations are not merely backdrops‚ but complex hubs of intrigue and danger․
Beyond these metropolises‚ numerous other significant sites await exploration‚ each with unique challenges and rewards․ Careful mapping and reconnaissance are vital for survival․ The PDF details these locations‚ offering crucial insights for navigating the treacherous Underdark landscape․
Gracklstugh: The City of Blades
Gracklstugh‚ a duergar stronghold‚ dominates Night Below’s landscape․ The PDF meticulously details its brutal architecture and cutthroat society‚ ruled by powerful merchant lords and driven by relentless industry․
Expect constant conflict between factions and a pervasive atmosphere of paranoia․ Navigating Gracklstugh requires shrewd diplomacy or overwhelming force․ The city’s intricate network of tunnels and forges presents both opportunities and deadly traps for unwary adventurers‚ as outlined in the campaign PDF․
Mantol-Derith: The City of Chains
Mantol-Derith‚ a drow city detailed within the Night Below PDF‚ stands as a chilling testament to Lolth’s power․ Ruled by a matriarchal society‚ it’s a labyrinth of intrigue‚ slavery‚ and religious fanaticism․
The PDF emphasizes the city’s oppressive atmosphere and the constant power struggles between noble houses․ Adventurers will face moral dilemmas and deadly challenges navigating its treacherous politics․ Expect encounters with cruel priestesses and enslaved populations‚ all vividly described in the campaign materials․

Other Significant Underdark Locations
Beyond Gracklstugh and Mantol-Derith‚ the Night Below PDF unveils a wealth of Underdark locales․ These range from ancient‚ forgotten ruins guarded by bizarre creatures to bustling trade outposts controlled by duergar clans․
The campaign material details unique environments‚ each presenting distinct challenges and opportunities for adventurers․ Expect to explore fungal forests‚ subterranean lakes‚ and cavern systems teeming with danger‚ all brought to life through detailed descriptions within the PDF․
Gameplay Mechanics Specific to Night Below
The Night Below PDF introduces mechanics tailored to the Underdark’s harsh environment․ Adapting to perpetual darkness and confined spaces is crucial‚ demanding innovative combat strategies․ Utilizing stealth and exploiting the environment become paramount for survival․

Players must manage resources carefully‚ as supplies are scarce and dangers lurk around every corner; The PDF emphasizes tactical decision-making‚ rewarding clever planning and punishing recklessness within the Underdark’s treacherous depths․
Adapting to the Underdark’s Challenges
The Night Below PDF necessitates adapting to unique Underdark challenges․ Perpetual darkness demands reliance on darkvision or alternative light sources‚ impacting combat and exploration․ Confined spaces favor tactical positioning and area-control spells․
Resource management is vital‚ as the Underdark offers limited supplies․ Players must contend with unusual creatures and navigate complex social dynamics within duergar and drow societies‚ as detailed in the PDF’s extensive lore․
Combat Strategies in Confined Spaces
The Night Below PDF’s encounters frequently occur in claustrophobic Underdark tunnels․ Prioritize choke point control and utilize spells affecting areas‚ not single targets․ Flanking becomes crucial‚ but be wary of allies hindering movement․
Melee characters should focus on positioning‚ while ranged attackers exploit limited sightlines․ Consider spells like Web or Fog Cloud to further restrict enemy movement‚ as detailed within the campaign’s tactical notes․
Utilizing Darkness and Stealth
The Night Below PDF heavily emphasizes darkness as a tactical element․ Characters proficient in Stealth gain significant advantages‚ exploiting the Underdark’s natural obscurity․ Darkvision is essential‚ but not foolproof; magical darkness can negate it․
Spells like Darkness and abilities creating concealment are invaluable․ Consider how creatures native to the Underdark utilize these conditions‚ as outlined in the campaign’s monster stat blocks․ Careful positioning and silent movement are key to survival․
The History of Night Below’s Development
Originally published by TSR in 1995‚ the Night Below PDF represents a classic Dungeons & Dragons adventure․ It was designed as a sprawling Underdark campaign for levels 1-10‚ offering a complex and challenging experience․
Later conversions and updates have refined the adventure‚ addressing balance issues and clarifying ambiguous rules․ Community contributions have further enhanced the PDF‚ providing maps and supplemental materials․ The adventure’s enduring popularity ensures continued support and adaptation․
Original Publication and Editions

Night Below was first released in 1995 by TSR as an adventure module for Advanced Dungeons & Dragons (AD&D)․ Designated as TSR 01125‚ it quickly became a favored campaign for players exploring the Underdark․
The initial publication offered a comprehensive experience‚ but subsequent editions have emerged through PDF conversions and community efforts․ These updates aim to improve clarity and accessibility‚ ensuring the adventure remains relevant for modern gaming groups․
Conversion and Updates
The original Night Below adventure has undergone significant conversion to PDF format‚ facilitating wider access and playability․ Community members have contributed extensively‚ creating organized sections within the document for easier navigation during gameplay․
These updates often include high-resolution maps‚ available through platforms like Patreon‚ enhancing the visual experience․ Conversion efforts also address outdated rules‚ adapting the campaign for contemporary Dungeons & Dragons systems․
Community Contributions and Resources

The Night Below PDF benefits immensely from dedicated community efforts․ Players and Dungeon Masters alike share resources‚ including detailed maps – often available via Patreon for free or in high resolution (8k versions)․
Online forums and websites host discussions‚ character sheets‚ and adapted rules‚ enriching the campaign experience․ These contributions demonstrate a passionate fanbase committed to preserving and enhancing this classic Underdark adventure for new generations of players․
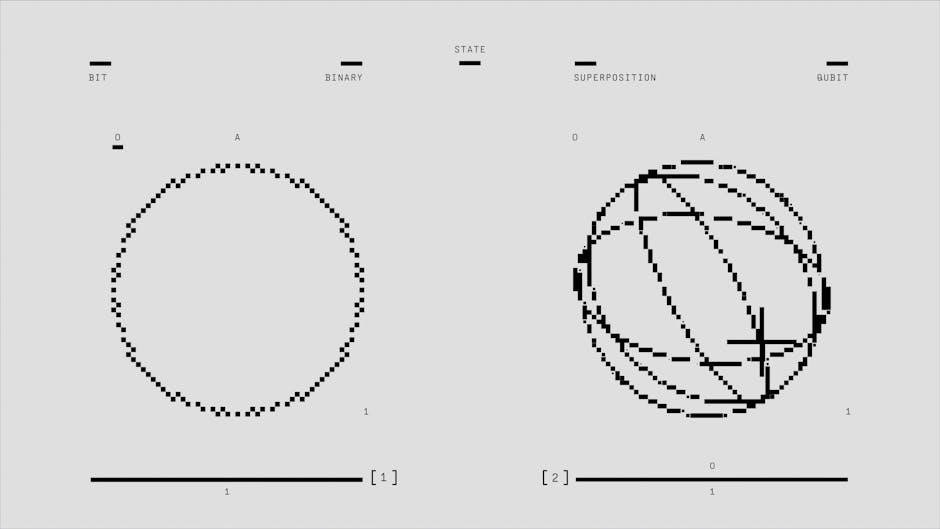
The Evolution of “Night” as a Time Expression

Historically‚ “at night” originated to denote a specific point in time‚ while “in the night” described a broader‚ less defined period․ The usage of prepositions evolved‚ impacting how we perceive nighttime․
Interestingly‚ the term “night-night‚” a more affectionate farewell‚ emerged in the 1930s-50s‚ showcasing the evolving nuances of expressing “good night․” Understanding these shifts provides context‚ even when delving into the darkness of the Night Below PDF campaign․
“At Night” vs․ “In the Night”: Usage Differences
The distinction between “at night” and “in the night” is subtle yet significant․ “At night” generally refers to nighttime as a general period‚ while “in the night” can denote events within a specific night․
Considering the Night Below PDF campaign‚ envisioning encounters “at night” suggests a consistent Underdark darkness‚ whereas “in the night” might describe a particular event unfolding during a single‚ perilous night within Gracklstugh․
Historical Origins of “Night” Terminology
The term “night” itself‚ denoting the period of darkness‚ has ancient roots‚ evolving alongside human perception of time․ Originally‚ “at night” signified a point in time‚ emerging in older linguistic structures․
Relating this to the Night Below PDF campaign‚ the Underdark’s perpetual darkness amplifies the significance of “night‚” becoming less a time marker and more a defining characteristic of the setting․ The campaign’s atmosphere inherently embodies the historical weight of the term․

Variations in Saying Goodnight (“Night-Night”)
While “good night” is standard‚ affectionate variations like “night-night” exist‚ conveying intimacy and closeness․ This nuanced expression‚ popular in personal relationships‚ contrasts sharply with the harsh realities of the Night Below PDF campaign’s Underdark․
Within the campaign’s grim setting‚ such tender farewells feel distant‚ highlighting the constant struggle for survival․ The Underdark offers little room for gentle goodnights‚ emphasizing the campaign’s perilous nature․